OTA updates are Over-the-Air updates of Software (SOTA) or Firmware (FOTA) on a remote asset, e.g. via WLAN or mobile networks. OTA update mechanisms are now a common feature for almost all smart phones, tablets, and similar devices. In automotive, some early adopters like Tesla have been pioneering OTA. It is expected that most OEMs will adopt OTA updates as a standard feature in the near future as well.
A great example for the use of OTA in automotive is the introduction of the Tesla 'Dog Mode', which aims to keep owners' pets at a comfortable temperature when left unattended. This feature is made available to Tesla owners on demand via OTA.
OTA Updates are a key capability of any AIoT product, since they allow to evolve the software deployed on the asset over time, gradually rolling out new functionality. If combined with an app store, OTA updates allow to tap into a rich developer community, which can add new functionalities and apps in many creative ways which sometimes have not been foreseen by the asset manufacturer and platform operator.
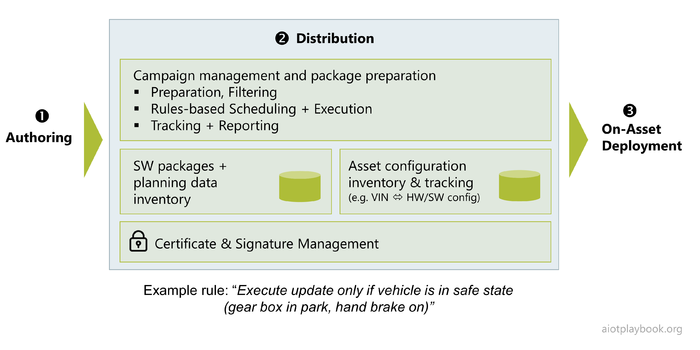
The figure above shows a typical OTA architecture for AIoT products. It all starts with the authoring (1) of new versions of software or firmware. This process can include deliveries from suppliers and sub-suppliers, which need to be integrated, tested and bundled. Next, the distribution component (2) is responsible for making the updates available in different regions, and coordinating the update campaigns. Finally, the on-asset deployment (3) is responsible for ensuring that the update is reaching its target.
Because OTA is becoming such an important feature of IoT and AIoT systems, a number of standards are emerging in this space. ISO 24089 aims to provide a standard architecture for OTA updates for road vehicles. The OMA DM protocol provides an integrated and extensible framework for OTA management. A number of existing standards describe specifically how to implement delta-updates for firmware, thus dramatically reducing the amount of data to be transferred to each device individually.
Distribution
The distribution component of an OTA platform must is typically responsible for package preparation and campaign management, as well as tracking and reporting. Campaign management can rely on complex rules to control updates to large amounts of devices or assets. For example, rules can help ensuring that assets such as road vehicles are not updated in critical situations (e.g. prevent updates while driving, or require the asset to not be in a remote area in case of update problems, etc.).
The typical components of the distribution tier include:
- Repository for firmware/software packages and planning data
- Asset inventory and update tracking / reporting
- Certificate & Signature Management
Deployment
Most OTA platforms include a dedicated update agent, which receives software/firmware updates from the remote distribution tier in the backend. Key functionality of the update agent typically includes:
- Download Management
- Certificate Validation
- Signature Validation
- Local Distribution
The local distribution from the update agent to the final target system can happen via a number of different local bus systems, including CAN, LIN, MOST, FlexRay, Ethernet, etc.
The actual target system can either be a lower-level controller (e.g. an ECU or TCU), or a high-end edge computer with own local storage, etc. For lower-level controllers, FOTA is sometime not only referring to updates to the embedded OS, but also to the - typically highly specialized - application logic. For higher-end on-asset computers, SOTA is referring to updates to generic applications.
Authors and Contributors
KAI HACKBARTH, BOSCH.IO
AUTHOR Kai Hackbarth is Business Owner Industrial at Bosch.IO, and also co-chair of the OTA SIG at the Industrial Internet Consortium. Kai has many years experience with IoT applications and architectures. He also has served as a Director of the OSGi Alliance for many years.
DIRK SLAMA
(Editor-in-Chief) CONTRIBUTOR Dirk Slama is VP and Chief Alliance Officer at Bosch Software Innovations (SI). Bosch SI is spearheading the Internet of Things (IoT) activities of Bosch, the global manufacturing and services group. Dirk has over 20 years experience in very large-scale distributed application projects and system integration, including SOA, BPM, M2M and most recently IoT. He is representing Bosch at the Industrial Internet Consortium and is active in the Industry 4.0 community. He holds an MBA from IMD Lausanne as well as a Diploma Degree in Computer Science from TU Berlin. |